Firestarter Firewall for Linux: Policies
This is the second of two posts about the Firestarter Firewall for Linux. The first, which includes download information, is here.
The main Firestarter interface includes tabs for Status (discussed in the previous post linked above), Events, and Policy. The Events tab shows connection attempts blocked by the firewall; it can be refined under Edit–>Preferences–>Events.
Most users, to the extent that they spend any time in the interface, will spend it configuring policies.
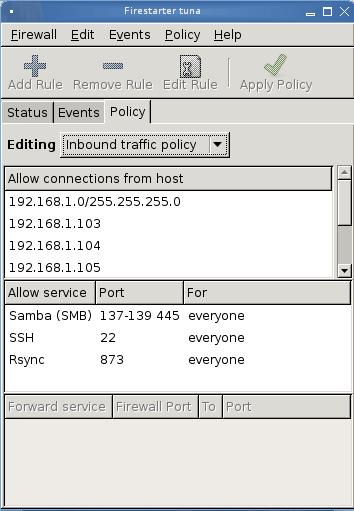
By default, Firestarter is “permissive” for outbound connections, meaning that all outbound connections are allowed, and “restrictive” for inbound connections, meaning that no inbound connections are allowed. This is just fine for email, websurfing, and other day-to-day computer usage.*
However, if you wish to use the computer as a server to allow other computers from both inside and outside your network to connect, you need to tell the firewall that the connections are okay. This includes both the network connection and the service (or port) connection.
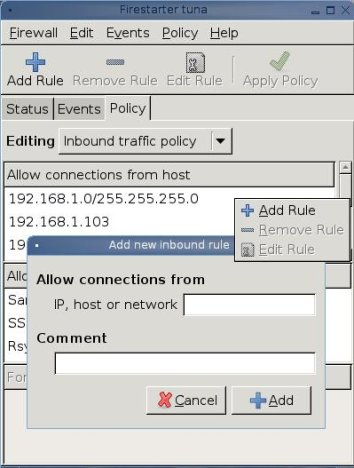
To allow inbound network connections, right-click in the “Allow Connections from Host” field, then click “Add Rule.” Type the ip address of network or host (device) to be allowed (“comments” are optional).
Here’s where I have noticed a quirk. On some of my computers, it has been enough to identify the allowed network (192.168.1.0/255.255.255.0). On others, I have had to type the individual addresses of the computers in the network, as shown in the picture above. I have not bothered to find out why, since I’m running a small home network with half a dozen boxes and it’s not a big deal; if I were running a business network, I would dig into this big time.
To edit or change the rule, highlight it, right-click, and select “Remove Rule” or “Edit Rule” from the pop-up menu.
Allowing a service is a similar process. Right click in the “Allow Service” window. When the pop-up appears, you may hit the drop-down arrow under “Allow Service–>Name” and select from the list of services; the default port(s) for the select service will be added to the list.
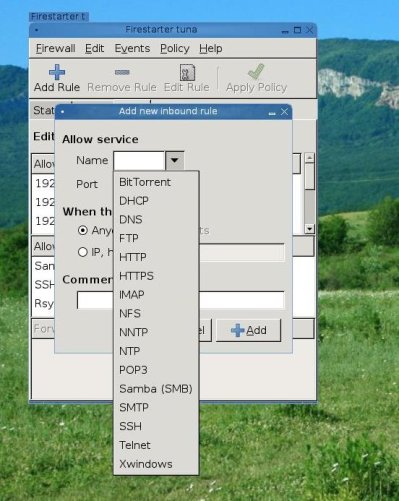
If you are not using the default ports or if you wish to add a service not in the list, such as some of the services for the Ekiga sip phone program, you can type in the service name and port number(s).
You can also specify whether to accept the service from anywhere, from a particular network, or even specific devices.
To implement the policy changes, go to the menu bar and click Policy–>Apply Policy. (You can set policy changes to take effect immediately in Edit–>Preferences).
Firestarter allows more in the way of configuration options, but most of them are irrelevant to the home user. You can learn more by downloading a copy of the handout I prepared for a presentation to my local LUG.
________________________
*In a business environment, it may be wise also to restrict outbound connections, allowing only selected ports and services.
I know of a hospital that maintains a public network and public computers for patients to use; the only open outbound port on the public network is port 80, to allow websurfing. Such restrictions, though, are normally managed at the router level, rather than at the computer level.



